Open-Source Vulnerabilities Management
Open-Source Vulnerabilities Management

4
1. Meaning and Concept
Open-Source Vulnerabilities Management refers to the process of identifying, assessing, mitigating, and monitoring security risks arising from the use of open-source software (OSS) components within applications.
Modern software relies heavily on OSS (often 70–90% of codebases), making vulnerability management a critical cybersecurity and legal compliance function.
2. Why It Matters
- Open-source libraries may contain known vulnerabilities (CVEs)
- Widely used packages create systemic risk (supply chain attacks)
- Organizations may face legal liability, regulatory penalties, and reputational harm
Famous examples include:
- Log4Shell vulnerability
- SolarWinds supply chain attack
3. Key Components of Vulnerability Management
(a) Inventory Management (SBOM)
- Maintain a Software Bill of Materials (SBOM) listing all dependencies.
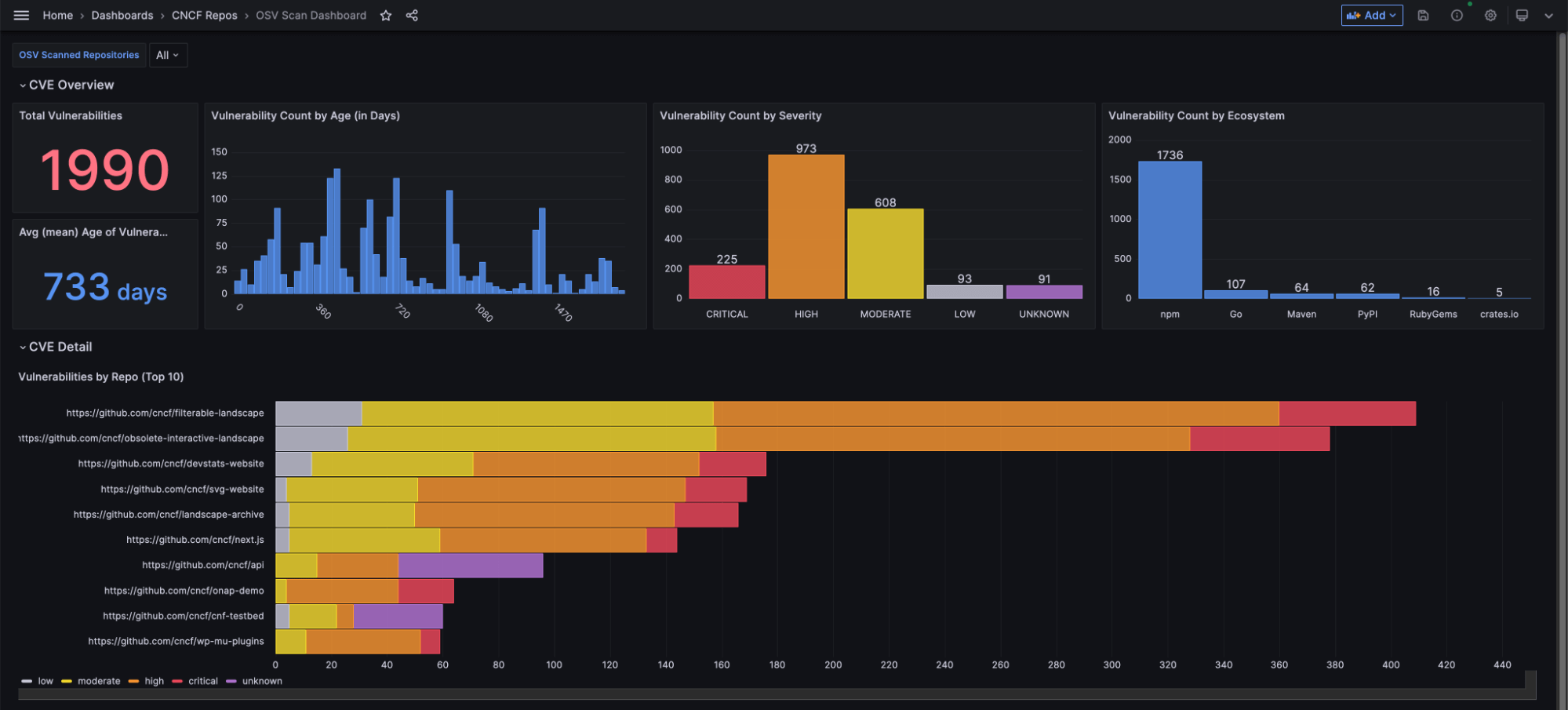
(b) Vulnerability Detection
- Use tools to scan for known vulnerabilities (e.g., CVE databases).
(c) Risk Assessment
- Evaluate severity using CVSS scores.
(d) Remediation
- Patch, upgrade, or replace vulnerable components.
(e) Continuous Monitoring
- Ongoing tracking of newly discovered vulnerabilities.
4. Lifecycle of Open-Source Vulnerability Management
Step 1: Identification
- Detect vulnerable components via scanning tools.
Step 2: Prioritization
- Rank vulnerabilities based on severity and exploitability.
Step 3: Remediation
- Apply patches or mitigations.
Step 4: Verification
- Confirm vulnerability is resolved.
Step 5: Reporting & Compliance
- Document actions for audits and regulators.
5. Legal and Regulatory Framework
- Data Protection Laws (e.g., GDPR-type frameworks)
- Cybersecurity Regulations (e.g., NIS Directive, India CERT-In guidelines)
- Software Licensing Laws (GPL, MIT, Apache licenses)
- Contractual Obligations (SLAs, warranties, indemnities)
Organizations must ensure:
- Secure software development practices
- Timely patching
- Disclosure of vulnerabilities when required
6. Common Risks
(a) Known Vulnerabilities
- Use of outdated libraries with published CVEs.
(b) Supply Chain Attacks
- Malicious code inserted into trusted packages.
(c) License Risks
- Improper use of OSS licenses leading to legal exposure.
(d) Lack of Visibility
- Hidden dependencies (“transitive dependencies”).
7. Case Laws Relevant to Open-Source Vulnerability Management
1. Google LLC v Oracle America Inc (2021)
- Concerned use of Java APIs.
- Supreme Court recognized fair use in software context.
- Highlights importance of OSS usage and licensing compliance.
2. Jacobsen v Katzer (2008)
- Enforced open-source license conditions.
- Court held that OSS licenses are legally binding.
- Critical for compliance in OSS usage.
3. Artifex Software Inc v Hancom Inc (2017)
- Concerned violation of GPL license.
- Court enforced dual licensing obligations.
- Relevant for license compliance risk in OSS.
4. Capitol Records LLC v ReDigi Inc (2018)
- Addressed digital distribution and reproduction rights.
- Though not OSS-specific, relevant for digital asset control and licensing.
5. Equifax Data Breach Litigation (2017–2020)
- Breach caused by unpatched open-source vulnerability (Apache Struts).
- Court held company accountable for failure to patch known vulnerabilities.
- Landmark case for cybersecurity negligence.
6. In re Target Corporation Customer Data Security Breach Litigation (2013)
- Data breach due to weak security controls.
- Established liability for inadequate cybersecurity practices.
7. FTC v Wyndham Worldwide Corporation (2015)
- FTC enforced cybersecurity standards.
- Court confirmed regulatory authority over unfair security practices.
- Relevant to failure in managing vulnerabilities.
8. Sony PlayStation Network Data Breach Litigation (2011)
- Massive breach due to security weaknesses.
- Highlighted duty to implement reasonable security measures.
8. Best Practices
(i) Adopt SBOM Frameworks
- Maintain transparency of all components.
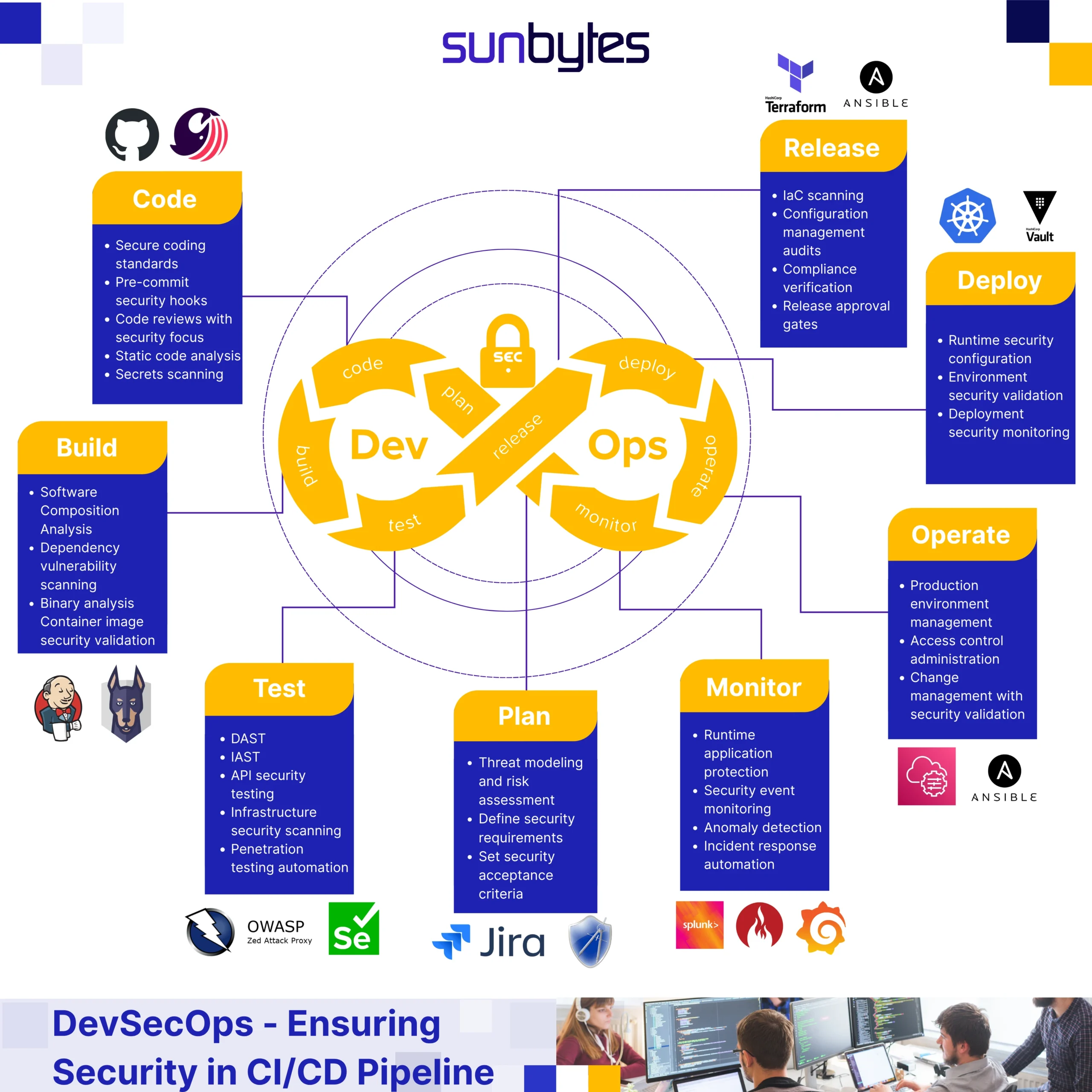
(ii) Automate Security Scanning
- Use DevSecOps tools for continuous monitoring.
(iii) Patch Management Policies
- Timely updates of vulnerable components.
(iv) Vendor and Dependency Management
- Assess third-party risks.
(v) Security Training
- Educate developers on secure coding practices.
9. Governance and Compliance Strategies
- Establish Open-Source Governance Policies
- Define risk ownership within organization
- Conduct regular security audits
- Implement incident response plans
- Ensure contractual safeguards with vendors
10. Emerging Trends
- Software Supply Chain Security (SSCS)
- Zero Trust Architecture
- AI-driven vulnerability detection
- Regulatory push for SBOM disclosure
- Global cybersecurity standardization
11. Conclusion
Open-source vulnerabilities management is no longer optional—it is a legal, operational, and cybersecurity necessity.
Courts and regulators increasingly emphasize:
- Timely patching of known vulnerabilities
- Strict compliance with OSS licenses
- Accountability for cybersecurity failures
- Proactive risk management
Organizations that fail to manage OSS risks effectively may face:
- Legal liability
- Financial penalties
- Reputational damage



comments